Data is invaluable in today’s digital age. Organizations rely on data to drive key business decisions and provide services. However, some of this data is highly sensitive and needs protection. This is where dynamic data masking comes in – obscuring the sensitive information to prevent unauthorized access. In this blog post, we’ll explore dynamic data masking as a powerful data privacy and protection tool.
Table of Contents
What is Dynamic Data Masking?
Dynamic Data Masking (DDM) obscures sensitive information during access requests, adapting in real-time based on user attributes, data values, and contextual factors, safeguarding privacy and security.
The Mechanism of Dynamic Data Masking
Dynamic data masking works by concealing sensitive data in real-time as it’s retrieved from the database. When a user or application queries the database, the DDM engine intercepts the query before it reaches the actual database. It analyzes the query to identify any sensitive data being requested.
The DDM engine then applies the appropriate masking rules to the sensitive data on-the-fly before returning the query results. The users or applications receive masked data without realizing the original values are obscured.
For example, if a query asks for user records including credit card numbers, the credit card numbers will be masked according to the format specified in the DDM rules. The rest of the data is returned unchanged.
The key advantage of DDM is it does not permanently alter or encrypt the original data in the database. The data remains intact within the database itself. Only when query results are returned does the masking occur. This is beneficial because privileged users or applications can still access original data when required.
The Dynamic data masking engine essentially acts as an abstraction layer between users and the real data. It applies context-aware masking dynamically based on the query, the data being requested, and the defined rules. This real-time masking prevents unauthorized access to sensitive data while allowing dynamic access to authorized users.
DDM rules can specify different data fields to mask and the masking format or algorithm to apply. For example, credit cards may be masked showing the last 4 digits while social security numbers are partially redacted. The rules provide granular control over data obfuscation.
The Effectiveness of Dynamic Data Masking
DDM provides an additional layer of control over sensitive data access, especially for read-only users. By concealing sensitive values, DDM limits data exposure. DDM is most effective when:
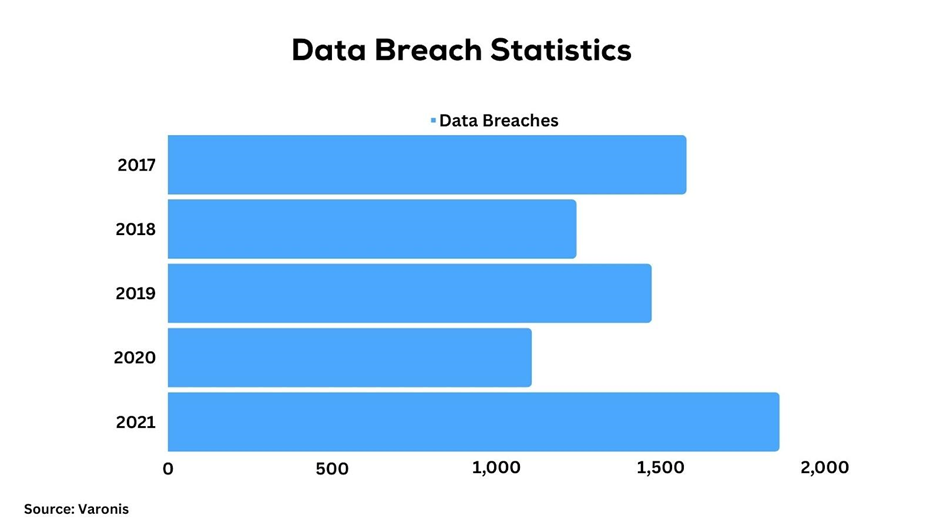
- Dealing with data breaches like personally identifiable information, financials, or healthcare records.
- Having read-only users that only need partial access to data. DDM allows seeing appropriate data.
- Used alongside other access controls like roles and permissions.
DDM prevents unauthorized access in real-time rather than attempting to monitor and audit misuse after it occurs. This real-time protection is a key advantage of the method.
Integrating Dynamic Data Masking with Other Data Protection Methods
DDM complements other data protection methods for a defense-in-depth approach. For example:
- DDM can be applied alongside data encryption to provide an additional safeguard for encrypted data. The data remains concealed even if decrypted.
- When used with data monitoring, DDM prevents misuse of data in real-time while monitoring can detect and alert unauthorized access attempts.
- Role-based access controls determine user access levels while DDM hides unauthorized data within authorized views.
DDM adds contextual protection based on data sensitivity. Other controls manage broader access requirements. Together they enhance data security.
Implementing Dynamic Data Masking
DDM can be implemented in various relational and non-relational databases like SQL Server, Oracle, MongoDB, and Cassandra. Databases provide built-in DDM capabilities or support integration with standalone DDM tools.
The key steps for implementing DDM are:
- Identify sensitive data fields to be masked.
- Define masking rules including masking functions like revealing part of data or using substitutions.
- Configure designated users that can view the original unmasked data.
- Apply the DDM rules at the database layer when queries retrieve data.
Proper implementation requires analyzing data usage patterns and classifying sensitivity levels. The DDM rules then align with usage needs and designated roles.
Limitations of Dynamic Data Masking
While DDM is a powerful data protection method, it also comes with some inherent limitations to be aware of:
- For databases with hundreds of tables and columns, configuring appropriate DDM rules can become very complex. Each sensitive field needs a custom rule for masking. This level of customization requires robust planning and mapping of data masking requirements.
- DDM only masks data as it is retrieved. But the original sensitive data remains intact and unencrypted within the database. Additional controls like database encryption are required to protect the raw data.
- DDM does not mask metadata such as database schemas, column names, or other structural data. Sensitive information may be inferred from metadata even if the data is masked. Using DDM alone may not fully obfuscate sensitive connections.
- DDM is less effective for encrypted data. Since encrypted data is not in plain text, applying masking rules becomes difficult. DDM should be applied before encryption to be fully effective.
- Applying DDM masking rules to every query leads to additional performance load. This can impact latency-sensitive transactions that require real-time data access. Careful optimization is required to minimize overhead.
- Since DDM operates at the database layer, any misconfiguration or bug can expose original sensitive data. Therefore, DDM should not be relied on as the only protection mechanism.
DDM should not be the sole data protection method. A layered security approach provides backup if DDM fails or is improperly configured.
Frequently Asked Questions
What is the main purpose of dynamic data masking?
The primary purpose of DDM is to limit exposure of sensitive data by concealing it from unauthorized users. DDM dynamically masks data as it is retrieved from the database.
How does dynamic data masking work in real-time?
DDM works by obscuring sensitive data on-the-fly after retrieval from the database and right before the data is presented to the requesting application or user. So DDM masks data in real-time.
Can DDM be used with other data protection methods?
Yes, DDM augments other data protection methods like encryption, role-based access, and data loss prevention. DDM provides an added layer of protection for sensitive data fields.
What is the difference between static and dynamic data masking?
Static Data Masking (SDM) permanently alters data at rest, replacing sensitive information. In contrast, Dynamic Data Masking (DDM) modifies data in transit, preserving the original at-rest data while securing sensitive details during access.
Conclusion
Dynamic data masking serves a vital role in sensitive data protection by concealing unauthorized data in real-time. DDM can be integrated with existing controls and database systems to dynamically mask sensitive fields as data is retrieved.
With proper implementation, dynamic data masking limits data exposure while allowing authorized access when required. Organizations dealing with sensitive data should actively consider implementing DDM as part of a comprehensive data privacy regime.
To learn more about implementing dynamic data masking, contact our data security experts for a consultation.

